IAM Roles as IaC for Secured Access Control of Business Accounts
- noviembre 21, 2019
Experts agree that the biggest security threat comes from inside the business. While reports of breaches from insider threats range from Security Intelligence’s 75% to 60% in an IBM survey, the overarching point is clear: intentionally or unintentionally employees present the biggest security risk. Identity and Access Management (IAM) helps address this threat by applying the principle of least privilege, keeping the business safe by allowing internal employees, external customers, and business partners access to only those resources necessary to perform their function. To illustrate, today we share the story of how a hospitality giant uses IAM roles as Infrastructure as Code (IaC) for secured access control for its team members.
With multiple AWS accounts, controlling access to them can be challenging. Keeping track of IAM roles and policies in each account also adds complexity. As the customer’s infrastructure team manually updates roles and policies through the AWS Console whenever there is an access request or updates to multiple accounts, the team spends countless hours on complex, distributed, manual tasks — tasks that lack control and open the door to human error.
The customer was interested in streamlining this process, with a goal to: convert IAM policies and roles into code and store them in a version control system (such as GitHub) so that IAM roles are created automatically in multiple accounts, saving time and effort.
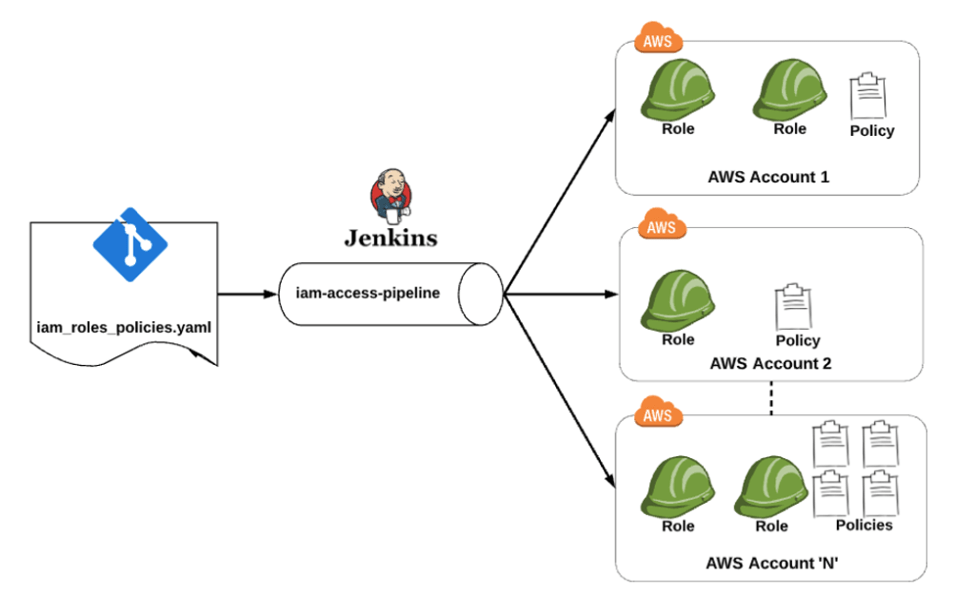
We helped the customer automate this process with a Jenkins pipeline that centralizes the IAM role, policy management, and deployment. This pipeline not only simplifies the role and policy management but also provides the ability to reuse code to add more roles through code. Before we look at the details of the IAM pipeline solution, let’s quickly review IAM Roles and Policies.
IAM Roles
IAM Roles allow you to define a set of permissions to access AWS resources. The roles are not attached to a particular user or group. Instead, IAM users, applications or services can programmatically assume a role to make AWS requests. Specifically, IAM Roles allow operators to perform three different functions:
- Create users in AWS’s identity management system and assign users individual security credentials.
- Request temporary security credentials to provide users access to AWS services and resources.
- Manage access for federated users, providing security credentials with configurable expirations for users in a corporate directory, thereby giving employees and applications secure access to resources in an AWS account without creating an IAM user account for them.
- With this background in mind, we created temporary security credentials for this organization’s team members, with the help of Okta’s Workforce Identity solution.
IAM Policies
Policies, defined in a policy document, determine the type of permissions that can be granted. When the policy document is attached to a user, group, or role, the permissions defined within that policy are automatically applied. For more information, refer to Policies and Permissions.
IAM Roles and Policies as IaC
For the customer, we created an IAM Access Git repository to store IAM roles and policies; we then created an IAM Access pipeline. As you can see here, the deployment pipeline automates the process of deploying IAM roles and policies, as defined in the repository, to multiple accounts.
IAM Roles and Policies as IaC Workflow
IAM Access Repository
The GitHub IAM Access Repository contains the following:
iam_roles_policies.yaml – This AWS CloudFormation template defines different IAM components like IAM Roles or IAM Policies. It can be used to modify — add, update or remove — any of the IAM roles and policies. This is the main file used to deploy IAM Resources in any AWS Account.
master-var.yaml – This is a file for variables and used for storing parameters that are consumed by the iam_roles_policies.yaml file.
pipeline-properties.yaml – This is a file for properties and has fields that are utilized by the Jenkinsfile to fill in certain variables. For example, the necessary account name is used for the stage (“Deploying IAM Roles/Policies to ${account_name}”).
IAM Access Pipeline
An IAM Access Pipeline was developed and deployed in a Jenkins instance. The purpose of the IAM Access Pipeline is to pull code from the IAM Access repository and deploy each IAM role and access policy (as defined in the CloudFormation template) to customer’s multiple AWS accounts.
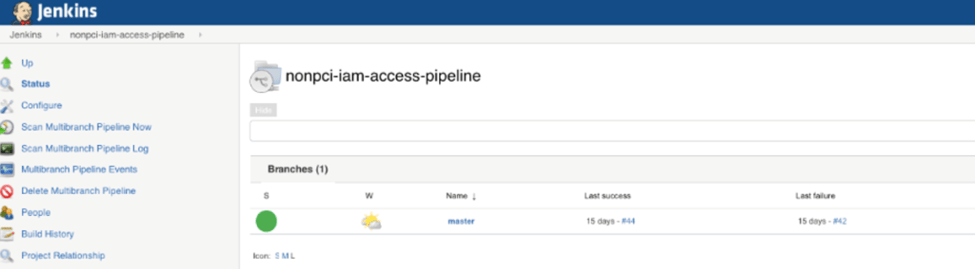
At one minute intervals, the pipeline monitors the repository for build triggers. If a role or policy was added to the iam_roles_policies.yaml file and properly merged through the master branch, the pipeline initiates a Jenkins build to generate the CloudFormation template. You can see here the pipeline stages as it deploys roles and policies across multiple AWS accounts.
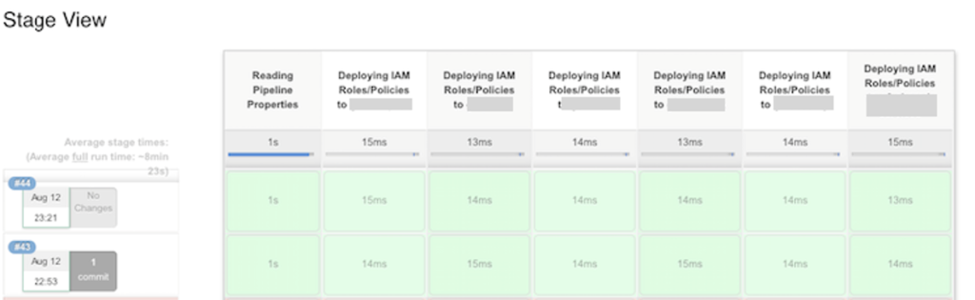
This solution helps the customer deploy and manage roles and policies with greater control, and fewer human errors across its nine AWS accounts.
AWS security best practices benefits
Using IAM Roles and Policies as IaC benefits the customer with a solution that is:
- Centralized and simplified. Now it is easy to deploy and manage roles and policies for multiple accounts as they are all accessible from one place.
- Saves time by removing the use of the AWS Console and the manual deployment of roles and policies in multiple accounts.
- Quick and easy to automatically add roles and policies with best practices, rather than relying on manual processes.
- Offers secure access control to accounts by tracking all related roles and policies.
- Reusable, flexible and customizable, allowing the customer to add more roles and policies through code, as needed.
- Auditable as IaC allows the customer to see how its code and roles evolve over time (Change Log).
Identity and Access Management (IAM) applies the principle of least privilege, keeping the business safe by allowing internal employees access to only those resources necessary to perform their function. Moreover, the IAM IaC solution protects this hospitality giant through temporary credentials that ensure former employees — or employees with changed roles — do not have access to systems where they can create unnecessary disruption.
In addition, IAM roles have their own advantages in defining a set of permissions to access AWS resources. By converting IAM policies and roles into code and storing them in a version control system, we can automatically create roles and policies in multiple accounts, saving time and effort.
*This was originally written by Flux7 Inc., which has become Flux7, an NTT DATA Services Company as of December 30, 2019
Subscribe to our blog




